linux安全篇:禁止频繁访问的ip访问nginx

点击「阅读原文」查看良许原创精品视频。
点击「阅读原文」查看良许原创精品视频。
实验环境
版本:redhat6.5
ip:172.16.1.100,172.16.10
软件:nginx
172.16.1.10部署nginx
[root@localhost tools]# ls
nginx-1.11.2.tar.gz
[root@localhost tools]# yum install gcc gcc-c++ make automake autoconf libtool pcre* zlib openssl openssl-devel
[root@localhost tools]# tar xf nginx-1.11.2.tar.gz
[root@localhost tools]# ls
nginx-1.11.2 nginx-1.11.2.tar.gz
[root@localhost tools]# cd nginx-1.11.2
[root@localhost nginx-1.11.2]# ls
auto CHANGES CHANGES.ru conf configure contrib html LICENSE man README src
[root@localhost nginx-1.11.2]# ./configure
[root@localhost nginx-1.11.2]# make
[root@localhost nginx-1.11.2]# make install
<以上代码可复制粘贴,可往左滑>
测试nginx服务
[root@localhost ~]# curl -I 172.16.1.100
HTTP/1.1 200 OK
Server: nginx/1.11.2
Date: Mon, 17 Aug 2020 09:36:29 GMT
Content-Type: text/html
Content-Length: 15
Last-Modified: Mon, 17 Aug 2020 09:36:19 GMT
Connection: keep-alive
ETag: "5f3a4f93-f"
Accept-Ranges: bytes
<以上代码可复制粘贴,可往左滑>
nginx 可以正常访问。
接下来,假设172.16.1.100是黑客主机,频繁访问nginx服务
模拟172.16.1.100访问10次172.16.1.10
172.16.1.100
[root@localhost ~]# ab -c 1 -n 10 http://172.16.1.10/
This is ApacheBench, Version 2.3 <$Revision: 1430300 $>
Copyright 1996 Adam Twiss, Zeus Technology Ltd, http://www.zeustech.net/
Licensed to The Apache Software Foundation, http://www.apache.org/
Benchmarking 172.16.1.10 (be patient).....done
Server Software: nginx/1.11.2
Server Hostname: 172.16.1.10
Server Port: 80
Document Path: /
Document Length: 612 bytes
Concurrency Level: 1
Time taken for tests: 0.016 seconds
Complete requests: 10
Failed requests: 0
Write errors: 0
Total transferred: 8450 bytes
HTML transferred: 6120 bytes
Requests per second: 617.02 [#/sec] (mean)
Time per request: 1.621 [ms] (mean)
Time per request: 1.621 [ms] (mean, across all concurrent requests)
Transfer rate: 509.16 [Kbytes/sec] received
Connection Times (ms)
min mean[+/-sd] median max
Connect: 0 1 0.3 0 1
Processing: 1 1 0.3 1 2
Waiting: 0 1 0.3 1 1
Total: 1 1 0.5 1 2
ERROR: The median and mean for the initial connection time are more than twice the standard
deviation apart. These results are NOT reliable.
Percentage of the requests served within a certain time (ms)
50% 1
66% 1
75% 1
80% 2
90% 2
95% 2
98% 2
99% 2
100% 2 (longest request)
查看nginx日志
172.16.1.10
[root@localhost ~]# tail /usr/local/nginx/logs/access.log
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
172.16.1.100 - - [26/Jul/2020:05:58:24 +0800] "GET / HTTP/1.0" 200 612 "-" "ApacheBench/2.3"
由此可见,一秒钟之内172.16.1.100访问了nginx10次,接下来禁止掉这个问题ip
通过iptables限制ip访问
172.16.1.10
[root@localhost ~]# iptables -I INPUT -s 172.16.1.100 -ptcp --dport 80 -j DROP
172.16.1.100
[root@localhost ~]# curl 172.16.1.10
curl: (7) Failed connect to 172.16.1.10:80; 连接超时
此时172.16.1.100再也不能访问nginx
nginx配置文件限制
172.16.1.10
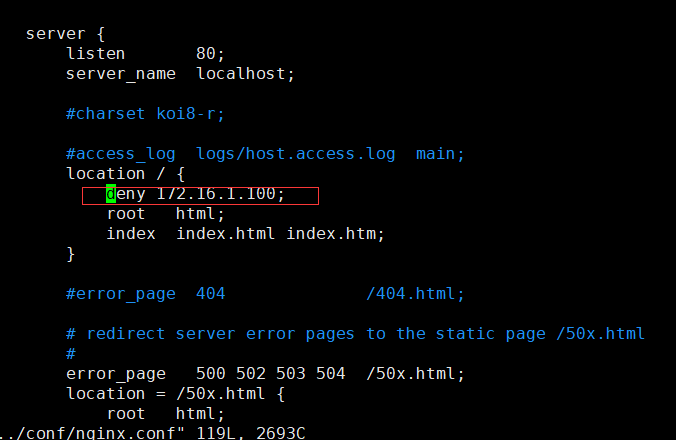
172.16.1.100
[root@localhost ~]# curl -I 172.16.1.10
HTTP/1.1 403 Forbidden
Server: nginx/1.11.2
Date: Sat, 25 Jul 2020 23:12:06 GMT
Content-Type: text/html
Content-Length: 169
Connection: keep-alive
<以上代码可复制粘贴,可往左滑>
总 结
以上就是两种简单的方法限制ip访问,还有许多方法可以利用工具进行ip限制。
推荐阅读:
5T技术资源大放送!包括但不限于:C/C++,Linux,Python,Java,PHP,人工智能,单片机,树莓派,等等。在公众号内回复「1024」,即可免费获取!!
评论
