常见的加密方式实例

前言
通常在我们测逻辑漏洞或写爬虫的时候,如果遇到前端加密,我们可以选择将加密算法拖出来,对自己调试的参数进行加密。
MD5加密实例
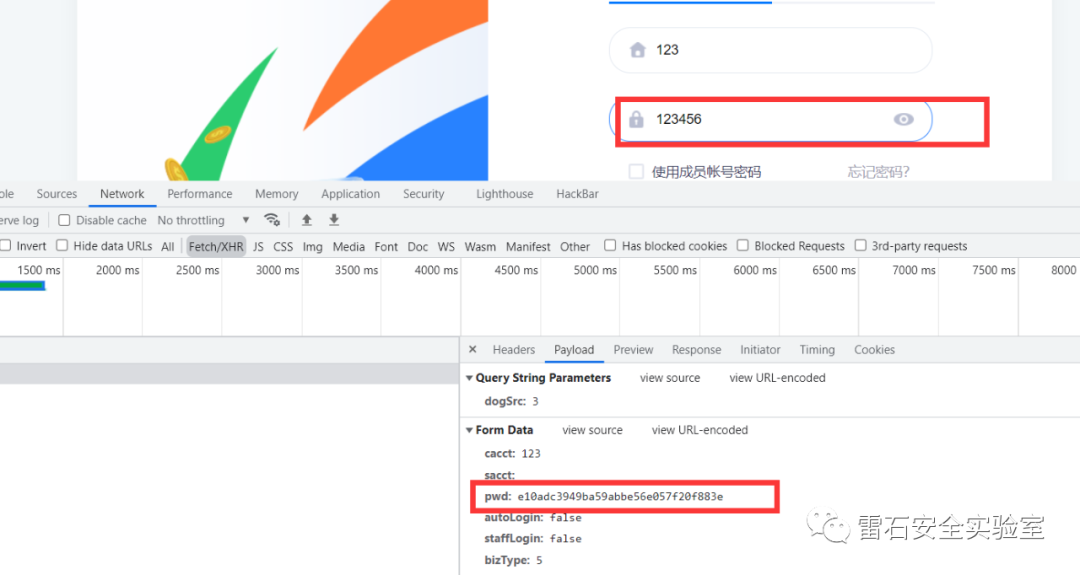
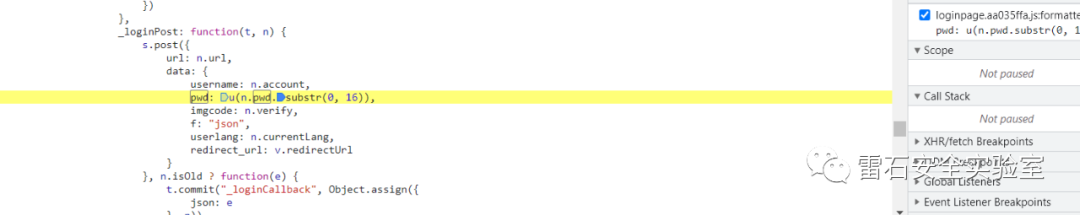
1.登录测试,获取到post参数
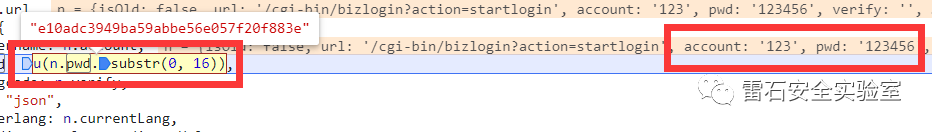
2.在疑似点下断,并再次发包
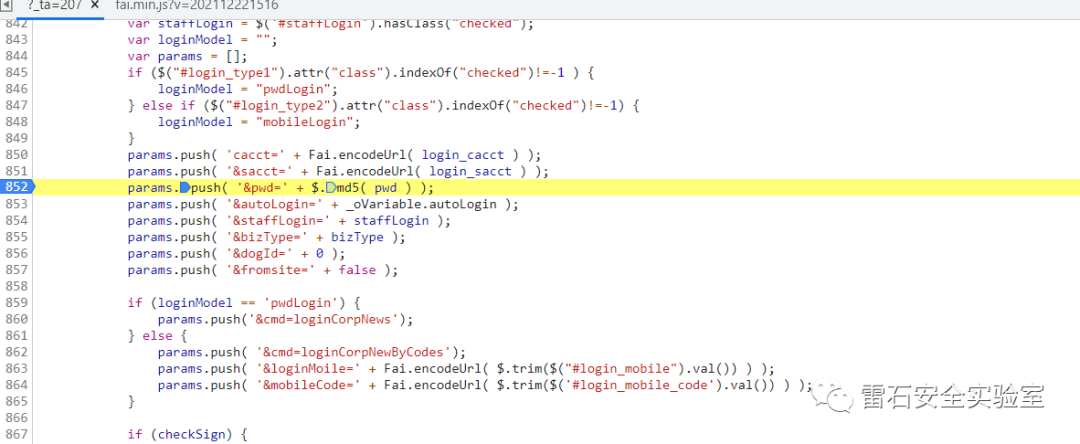
3.查看此处值与加密后的值相同,所以这个就是加密算法
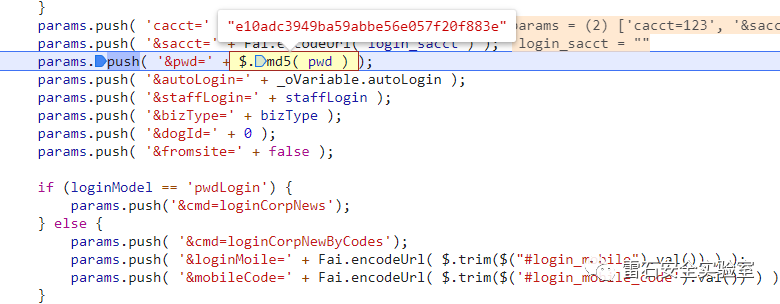
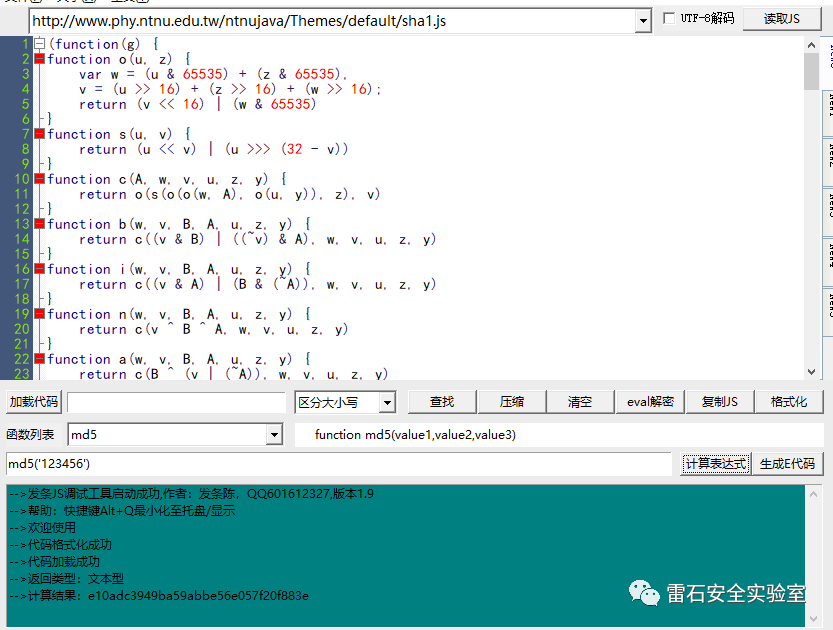
4.这是一个闭包函数,实现加密算法
~这里可以直接用md5进行加密测试,但不排除他命名为md5(),实际上自己实现的加密算法。~
(function(g) {
function o(u, z) {
var w = (u & 65535) + (z & 65535)
, v = (u >> 16) + (z >> 16) + (w >> 16);
return (v << 16) | (w & 65535)
}
function s(u, v) {
return (u << v) | (u >>> (32 - v))
}
function c(A, w, v, u, z, y) {
return o(s(o(o(w, A), o(u, y)), z), v)
}
function b(w, v, B, A, u, z, y) {
return c((v & B) | ((~v) & A), w, v, u, z, y)
}
function i(w, v, B, A, u, z, y) {
return c((v & A) | (B & (~A)), w, v, u, z, y)
}
function n(w, v, B, A, u, z, y) {
return c(v ^ B ^ A, w, v, u, z, y)
}
function a(w, v, B, A, u, z, y) {
return c(B ^ (v | (~A)), w, v, u, z, y)
}
function d(F, A) {
F[A >> 5] |= 128 << ((A) % 32);
F[(((A + 64) >>> 9) << 4) + 14] = A;
var w, z, y, v, u, E = 1732584193, D = -271733879, C = -1732584194, B = 271733878;
for (w = 0; w < F.length; w += 16) {
z = E;
y = D;
v = C;
u = B;
E = b(E, D, C, B, F[w], 7, -680876936);
B = b(B, E, D, C, F[w + 1], 12, -389564586);
C = b(C, B, E, D, F[w + 2], 17, 606105819);
D = b(D, C, B, E, F[w + 3], 22, -1044525330);
E = b(E, D, C, B, F[w + 4], 7, -176418897);
B = b(B, E, D, C, F[w + 5], 12, 1200080426);
C = b(C, B, E, D, F[w + 6], 17, -1473231341);
D = b(D, C, B, E, F[w + 7], 22, -45705983);
E = b(E, D, C, B, F[w + 8], 7, 1770035416);
B = b(B, E, D, C, F[w + 9], 12, -1958414417);
C = b(C, B, E, D, F[w + 10], 17, -42063);
D = b(D, C, B, E, F[w + 11], 22, -1990404162);
E = b(E, D, C, B, F[w + 12], 7, 1804603682);
B = b(B, E, D, C, F[w + 13], 12, -40341101);
C = b(C, B, E, D, F[w + 14], 17, -1502002290);
D = b(D, C, B, E, F[w + 15], 22, 1236535329);
E = i(E, D, C, B, F[w + 1], 5, -165796510);
B = i(B, E, D, C, F[w + 6], 9, -1069501632);
C = i(C, B, E, D, F[w + 11], 14, 643717713);
D = i(D, C, B, E, F[w], 20, -373897302);
E = i(E, D, C, B, F[w + 5], 5, -701558691);
B = i(B, E, D, C, F[w + 10], 9, 38016083);
C = i(C, B, E, D, F[w + 15], 14, -660478335);
D = i(D, C, B, E, F[w + 4], 20, -405537848);
E = i(E, D, C, B, F[w + 9], 5, 568446438);
B = i(B, E, D, C, F[w + 14], 9, -1019803690);
C = i(C, B, E, D, F[w + 3], 14, -187363961);
D = i(D, C, B, E, F[w + 8], 20, 1163531501);
E = i(E, D, C, B, F[w + 13], 5, -1444681467);
B = i(B, E, D, C, F[w + 2], 9, -51403784);
C = i(C, B, E, D, F[w + 7], 14, 1735328473);
D = i(D, C, B, E, F[w + 12], 20, -1926607734);
E = n(E, D, C, B, F[w + 5], 4, -378558);
B = n(B, E, D, C, F[w + 8], 11, -2022574463);
C = n(C, B, E, D, F[w + 11], 16, 1839030562);
D = n(D, C, B, E, F[w + 14], 23, -35309556);
E = n(E, D, C, B, F[w + 1], 4, -1530992060);
B = n(B, E, D, C, F[w + 4], 11, 1272893353);
C = n(C, B, E, D, F[w + 7], 16, -155497632);
D = n(D, C, B, E, F[w + 10], 23, -1094730640);
E = n(E, D, C, B, F[w + 13], 4, 681279174);
B = n(B, E, D, C, F[w], 11, -358537222);
C = n(C, B, E, D, F[w + 3], 16, -722521979);
D = n(D, C, B, E, F[w + 6], 23, 76029189);
E = n(E, D, C, B, F[w + 9], 4, -640364487);
B = n(B, E, D, C, F[w + 12], 11, -421815835);
C = n(C, B, E, D, F[w + 15], 16, 530742520);
D = n(D, C, B, E, F[w + 2], 23, -995338651);
E = a(E, D, C, B, F[w], 6, -198630844);
B = a(B, E, D, C, F[w + 7], 10, 1126891415);
C = a(C, B, E, D, F[w + 14], 15, -1416354905);
D = a(D, C, B, E, F[w + 5], 21, -57434055);
E = a(E, D, C, B, F[w + 12], 6, 1700485571);
B = a(B, E, D, C, F[w + 3], 10, -1894986606);
C = a(C, B, E, D, F[w + 10], 15, -1051523);
D = a(D, C, B, E, F[w + 1], 21, -2054922799);
E = a(E, D, C, B, F[w + 8], 6, 1873313359);
B = a(B, E, D, C, F[w + 15], 10, -30611744);
C = a(C, B, E, D, F[w + 6], 15, -1560198380);
D = a(D, C, B, E, F[w + 13], 21, 1309151649);
E = a(E, D, C, B, F[w + 4], 6, -145523070);
B = a(B, E, D, C, F[w + 11], 10, -1120210379);
C = a(C, B, E, D, F[w + 2], 15, 718787259);
D = a(D, C, B, E, F[w + 9], 21, -343485551);
E = o(E, z);
D = o(D, y);
C = o(C, v);
B = o(B, u)
}
return [E, D, C, B]
}
function p(v) {
var w, u = "";
for (w = 0; w < v.length * 32; w += 8) {
u += String.fromCharCode((v[w >> 5] >>> (w % 32)) & 255)
}
return u
}
function j(v) {
var w, u = [];
u[(v.length >> 2) - 1] = undefined;
for (w = 0; w < u.length; w += 1) {
u[w] = 0
}
for (w = 0; w < v.length * 8; w += 8) {
u[w >> 5] |= (v.charCodeAt(w / 8) & 255) << (w % 32)
}
return u
}
function k(u) {
return p(d(j(u), u.length * 8))
}
function f(w, z) {
var v, y = j(w), u = [], x = [], A;
u[15] = x[15] = undefined;
if (y.length > 16) {
y = d(y, w.length * 8)
}
for (v = 0; v < 16; v += 1) {
u[v] = y[v] ^ 909522486;
x[v] = y[v] ^ 1549556828
}
A = d(u.concat(j(z)), 512 + z.length * 8);
return p(d(x.concat(A), 512 + 128))
}
function t(w) {
var z = "0123456789abcdef", v = "", u, y;
for (y = 0; y < w.length; y += 1) {
u = w.charCodeAt(y);
v += z.charAt((u >>> 4) & 15) + z.charAt(u & 15)
}
return v
}
function m(u) {
return unescape(encodeURIComponent(u))
}
function q(u) {
return k(m(u))
}
function l(u) {
return t(q(u))
}
function h(u, v) {
return f(m(u), m(v))
}
function r(u, v) {
return t(h(u, v))
}
g.md5 = function(v, w, u) {
if (!w) {
if (!u) {
return l(v)
} else {
return q(v)
}
}
if (!u) {
return r(w, v)
} else {
return h(w, v)
}
}
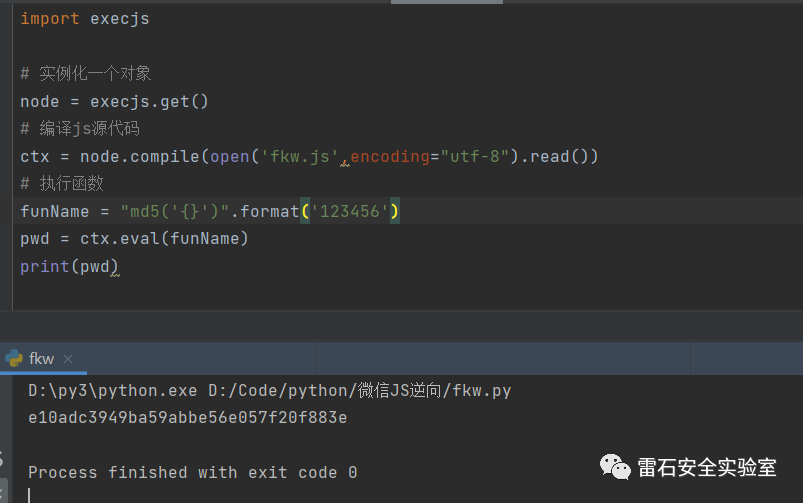
}(typeof jQuery === "function" ? jQuery : this));5.调试这段代码
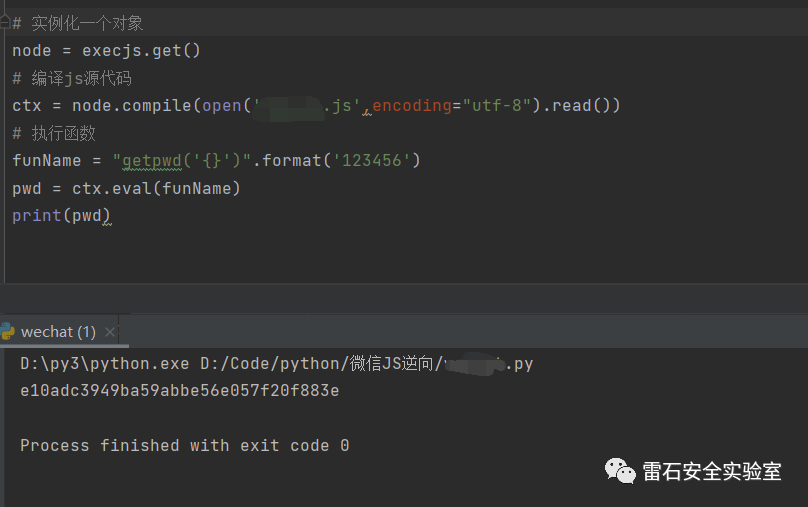
6.python执行
RSA非对称密钥加密实例
1.登录发包
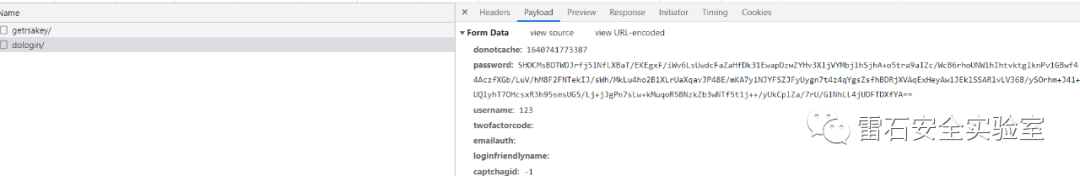
2.疑似点下断
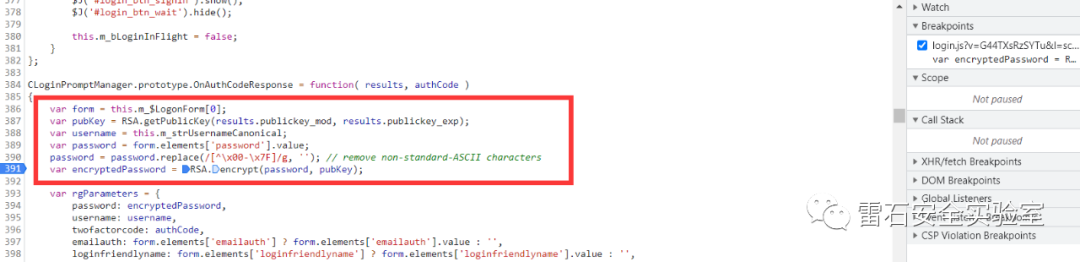
3.查找加密算法
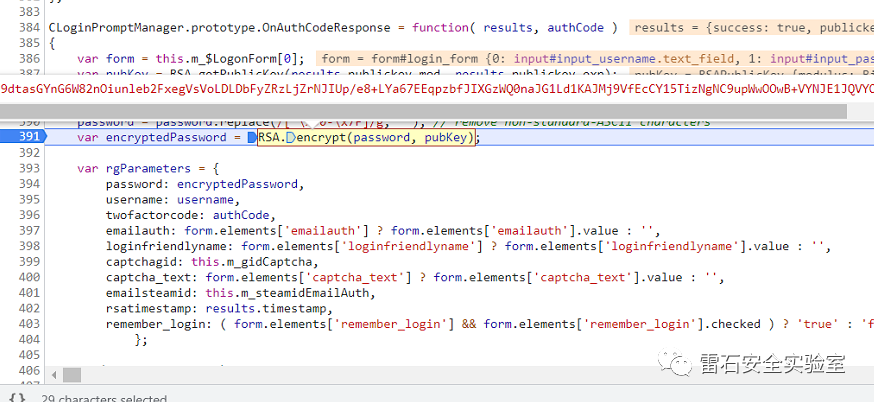
4.加密算法实现and调试
var RSAPublicKey = function($modulus_hex, $encryptionExponent_hex) {
this.modulus = new BigInteger( $modulus_hex, 16);
this.encryptionExponent = new BigInteger( $encryptionExponent_hex, 16);
};
var Base64 = {
base64: "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=",
encode: function($input) {
if (!$input) {
return false;
}
var $output = "";
var $chr1, $chr2, $chr3;
var $enc1, $enc2, $enc3, $enc4;
var $i = 0;
do {
$chr1 = $input.charCodeAt($i++);
$chr2 = $input.charCodeAt($i++);
$chr3 = $input.charCodeAt($i++);
$enc1 = $chr1 >> 2;
$enc2 = (($chr1 & 3) << 4) | ($chr2 >> 4);
$enc3 = (($chr2 & 15) << 2) | ($chr3 >> 6);
$enc4 = $chr3 & 63;
if (isNaN($chr2)) $enc3 = $enc4 = 64;
else if (isNaN($chr3)) $enc4 = 64;
$output += this.base64.charAt($enc1) + this.base64.charAt($enc2) + this.base64.charAt($enc3) + this.base64.charAt($enc4);
} while ($i < $input.length);
return $output;
},
decode: function($input) {
if(!$input) return false;
$input = $input.replace(/[^A-Za-z0-9\+\/\=]/g, "");
var $output = "";
var $enc1, $enc2, $enc3, $enc4;
var $i = 0;
do {
$enc1 = this.base64.indexOf($input.charAt($i++));
$enc2 = this.base64.indexOf($input.charAt($i++));
$enc3 = this.base64.indexOf($input.charAt($i++));
$enc4 = this.base64.indexOf($input.charAt($i++));
$output += String.fromCharCode(($enc1 << 2) | ($enc2 >> 4));
if ($enc3 != 64) $output += String.fromCharCode((($enc2 & 15) << 4) | ($enc3 >> 2));
if ($enc4 != 64) $output += String.fromCharCode((($enc3 & 3) << 6) | $enc4);
} while ($i < $input.length);
return $output;
}
};
var Hex = {
hex: "0123456789abcdef",
encode: function($input) {
if(!$input) return false;
var $output = "";
var $k;
var $i = 0;
do {
$k = $input.charCodeAt($i++);
$output += this.hex.charAt(($k >> 4) &0xf) + this.hex.charAt($k & 0xf);
} while ($i < $input.length);
return $output;
},
decode: function($input) {
if(!$input) return false;
$input = $input.replace(/[^0-9abcdef]/g, "");
var $output = "";
var $i = 0;
do {
$output += String.fromCharCode(((this.hex.indexOf($input.charAt($i++)) << 4) & 0xf0) | (this.hex.indexOf($input.charAt($i++)) & 0xf));
} while ($i < $input.length);
return $output;
}
};
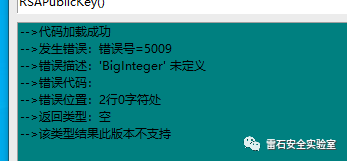
BigInteger未定义,查找这个函数实现并贴上去
function bnpCopyTo(r) {
for(var i = this.t-1; i >= 0; --i) r[i] = this[i];
r.t = this.t;
r.s = this.s;
}
// (protected) set from integer value x, -DV <= x < DV
function bnpFromInt(x) {
this.t = 1;
this.s = (x<0)?-1:0;
if(x > 0) this[0] = x;
else if(x < -1) this[0] = x+DV;
else this.t = 0;
}
// return bigint initialized to value
function nbv(i) { var r = nbi(); r.fromInt(i); return r; }
// (protected) set from string and radix
function bnpFromString(s,b) {
var k;
if(b == 16) k = 4;
else if(b == 8) k = 3;
else if(b == 256) k = 8; // byte array
else if(b == 2) k = 1;
else if(b == 32) k = 5;
else if(b == 4) k = 2;
else { this.fromRadix(s,b); return; }
this.t = 0;
this.s = 0;
var i = s.length, mi = false, sh = 0;
while(--i >= 0) {
var x = (k==8)?s[i]&0xff:intAt(s,i);
if(x < 0) {
if(s.charAt(i) == "-") mi = true;
continue;
}
mi = false;
if(sh == 0)
this[this.t++] = x;
else if(sh+k > this.DB) {
this[this.t-1] |= (x&((1<<(this.DB-sh))-1))< this[this.t++] = (x>>(this.DB-sh));
}
else
this[this.t-1] |= x< sh += k;
if(sh >= this.DB) sh -= this.DB;
}
if(k == 8 && (s[0]&0x80) != 0) {
this.s = -1;
if(sh > 0) this[this.t-1] |= ((1<<(this.DB-sh))-1)< }
this.clamp();
if(mi) BigInteger.ZERO.subTo(this,this);
}
// (protected) clamp off excess high words
function bnpClamp() {
var c = this.s&this.DM;
while(this.t > 0 && this[this.t-1] == c) --this.t;
}
// (public) return string representation in given radix
function bnToString(b) {
if(this.s < 0) return "-"+this.negate().toString(b);
var k;
if(b == 16) k = 4;
else if(b == 8) k = 3;
else if(b == 2) k = 1;
else if(b == 32) k = 5;
else if(b == 4) k = 2;
else return this.toRadix(b);
var km = (1<false, r = "", i = this.t;
var p = this.DB-(i*this.DB)%k;
if(i-- > 0) {
if(p < this.DB && (d = this[i]>>p) > 0) { m = true; r = int2char(d); }
while(i >= 0) {
if(p < k) {
d = (this[i]&((1< d |= this[--i]>>(p+=this.DB-k);
}
else {
d = (this[i]>>(p-=k))&km;
if(p <= 0) { p += this.DB; --i; }
}
if(d > 0) m = true;
if(m) r += int2char(d);
}
}
return m?r:"0";
}
// (public) -this
function bnNegate() { var r = nbi(); BigInteger.ZERO.subTo(this,r); return r; }
// (public) |this|
function bnAbs() { return (this.s<0)?this.negate():this; }
// (public) return + if this > a, - if this < a, 0 if equal
function bnCompareTo(a) {
var r = this.s-a.s;
if(r != 0) return r;
var i = this.t;
r = i-a.t;
if(r != 0) return r;
while(--i >= 0) if((r=this[i]-a[i]) != 0) return r;
return 0;
}
// returns bit length of the integer x
function nbits(x) {
var r = 1, t;
if((t=x>>>16) != 0) { x = t; r += 16; }
if((t=x>>8) != 0) { x = t; r += 8; }
if((t=x>>4) != 0) { x = t; r += 4; }
if((t=x>>2) != 0) { x = t; r += 2; }
if((t=x>>1) != 0) { x = t; r += 1; }
return r;
}
// (public) return the number of bits in "this"
function bnBitLength() {
if(this.t <= 0) return 0;
return this.DB*(this.t-1)+nbits(this[this.t-1]^(this.s&this.DM));
}
// (protected) r = this << n*DB
function bnpDLShiftTo(n,r) {
var i;
for(i = this.t-1; i >= 0; --i) r[i+n] = this[i];
for(i = n-1; i >= 0; --i) r[i] = 0;
r.t = this.t+n;
r.s = this.s;
}
// (protected) r = this >> n*DB
function bnpDRShiftTo(n,r) {
for(var i = n; i < this.t; ++i) r[i-n] = this[i];
r.t = Math.max(this.t-n,0);
r.s = this.s;
}
// (protected) r = this << n
function bnpLShiftTo(n,r) {
var bs = n%this.DB;
var cbs = this.DB-bs;
var bm = (1< var ds = Math.floor(n/this.DB), c = (this.s< for(i = this.t-1; i >= 0; --i) {
r[i+ds+1] = (this[i]>>cbs)|c;
c = (this[i]&bm)< }
for(i = ds-1; i >= 0; --i) r[i] = 0;
r[ds] = c;
r.t = this.t+ds+1;
r.s = this.s;
r.clamp();
}
// (protected) r = this >> n
function bnpRShiftTo(n,r) {
r.s = this.s;
var ds = Math.floor(n/this.DB);
if(ds >= this.t) { r.t = 0; return; }
var bs = n%this.DB;
var cbs = this.DB-bs;
var bm = (1< r[0] = this[ds]>>bs;
for(var i = ds+1; i < this.t; ++i) {
r[i-ds-1] |= (this[i]&bm)< r[i-ds] = this[i]>>bs;
}
if(bs > 0) r[this.t-ds-1] |= (this.s&bm)< r.t = this.t-ds;
r.clamp();
}
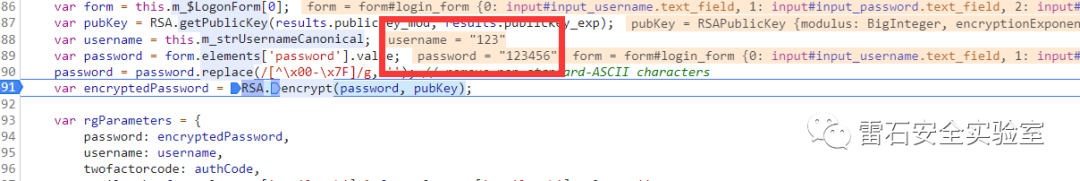
5.调试加密算法

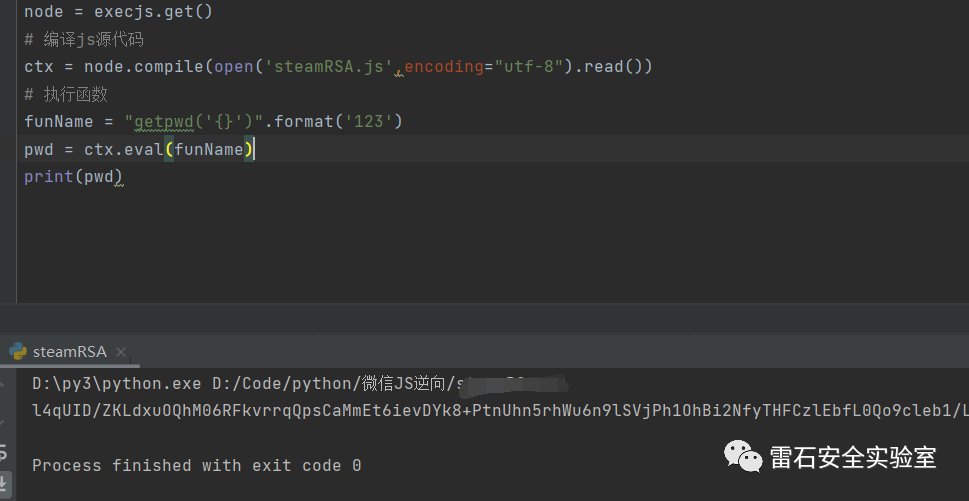
6.python执行
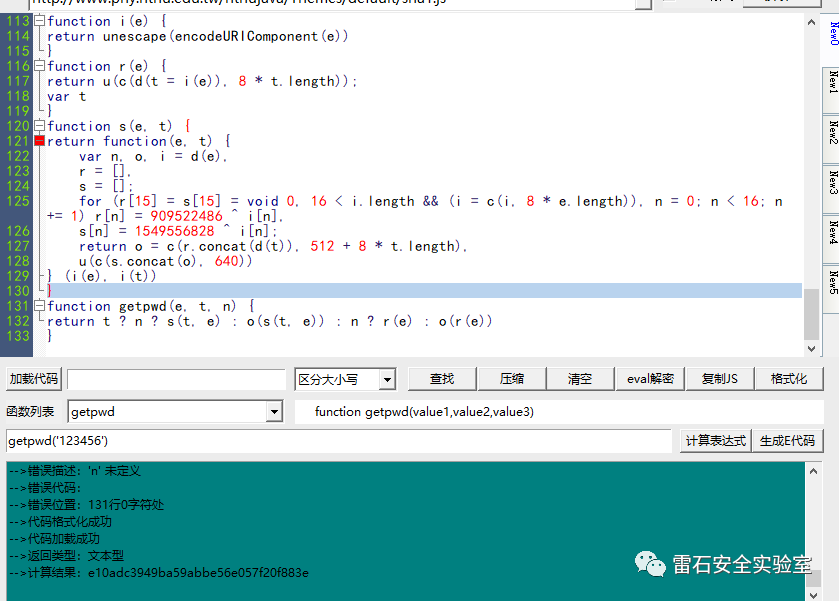
自写加密算法加密实例
1.登录发包
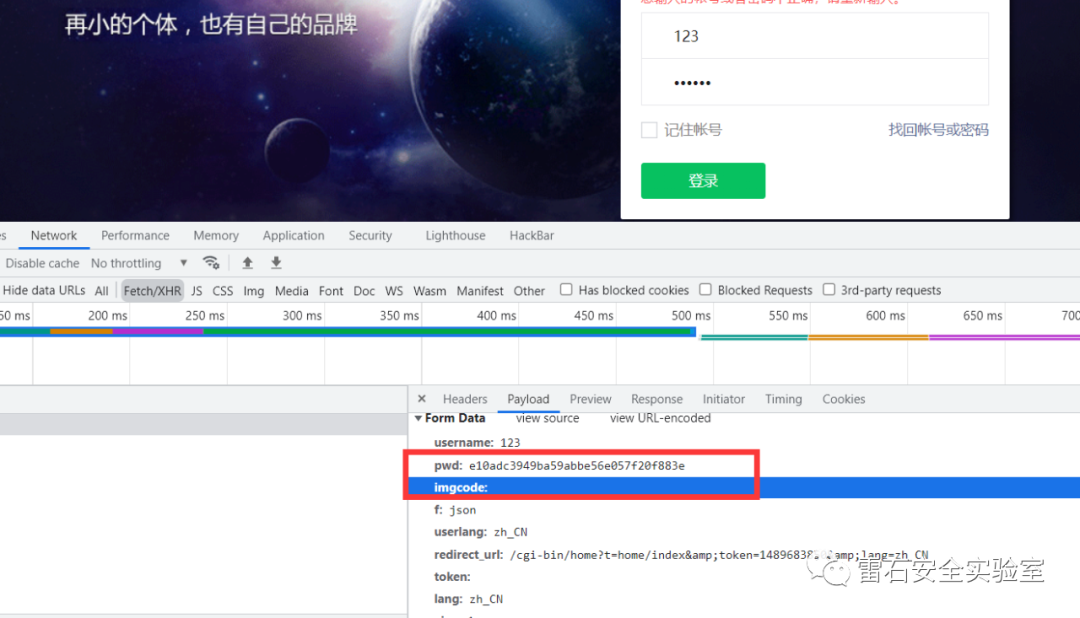
2.疑似点下断调试
3.查找加密算法
4.加密算法实现
function p(e, t) {
var n = (65535 & e) + (65535 & t);
return (e >> 16) + (t >> 16) + (n >> 16) << 16 | 65535 & n
}
function a(e, t, n, o, i, r) {
return p((s = p(p(t, e), p(o, r))) << (a = i) | s >>> 32 - a, n);
var s, a
}
function l(e, t, n, o, i, r, s) {
return a(t & n | ~t & o, e, t, i, r, s)
}
function m(e, t, n, o, i, r, s) {
return a(t & o | n & ~o, e, t, i, r, s)
}
function f(e, t, n, o, i, r, s) {
return a(t ^ n ^ o, e, t, i, r, s)
}
function g(e, t, n, o, i, r, s) {
return a(n ^ (t | ~o), e, t, i, r, s)
}
function c(e, t) {
e[t >> 5] |= 128 << t % 32,
e[14 + (t + 64 >>> 9 << 4)] = t;
var n, o, i, r, s, a = 1732584193,
c = -271733879,
u = -1732584194,
d = 271733878;
for (n = 0; n < e.length; n += 16) a = l(o = a, i = c, r = u, s = d, e[n], 7, -680876936),
d = l(d, a, c, u, e[n + 1], 12, -389564586),
u = l(u, d, a, c, e[n + 2], 17, 606105819),
c = l(c, u, d, a, e[n + 3], 22, -1044525330),
a = l(a, c, u, d, e[n + 4], 7, -176418897),
d = l(d, a, c, u, e[n + 5], 12, 1200080426),
u = l(u, d, a, c, e[n + 6], 17, -1473231341),
c = l(c, u, d, a, e[n + 7], 22, -45705983),
a = l(a, c, u, d, e[n + 8], 7, 1770035416),
d = l(d, a, c, u, e[n + 9], 12, -1958414417),
u = l(u, d, a, c, e[n + 10], 17, -42063),
c = l(c, u, d, a, e[n + 11], 22, -1990404162),
a = l(a, c, u, d, e[n + 12], 7, 1804603682),
d = l(d, a, c, u, e[n + 13], 12, -40341101),
u = l(u, d, a, c, e[n + 14], 17, -1502002290),
a = m(a, c = l(c, u, d, a, e[n + 15], 22, 1236535329), u, d, e[n + 1], 5, -165796510),
d = m(d, a, c, u, e[n + 6], 9, -1069501632),
u = m(u, d, a, c, e[n + 11], 14, 643717713),
c = m(c, u, d, a, e[n], 20, -373897302),
a = m(a, c, u, d, e[n + 5], 5, -701558691),
d = m(d, a, c, u, e[n + 10], 9, 38016083),
u = m(u, d, a, c, e[n + 15], 14, -660478335),
c = m(c, u, d, a, e[n + 4], 20, -405537848),
a = m(a, c, u, d, e[n + 9], 5, 568446438),
d = m(d, a, c, u, e[n + 14], 9, -1019803690),
u = m(u, d, a, c, e[n + 3], 14, -187363961),
c = m(c, u, d, a, e[n + 8], 20, 1163531501),
a = m(a, c, u, d, e[n + 13], 5, -1444681467),
d = m(d, a, c, u, e[n + 2], 9, -51403784),
u = m(u, d, a, c, e[n + 7], 14, 1735328473),
a = f(a, c = m(c, u, d, a, e[n + 12], 20, -1926607734), u, d, e[n + 5], 4, -378558),
d = f(d, a, c, u, e[n + 8], 11, -2022574463),
u = f(u, d, a, c, e[n + 11], 16, 1839030562),
c = f(c, u, d, a, e[n + 14], 23, -35309556),
a = f(a, c, u, d, e[n + 1], 4, -1530992060),
d = f(d, a, c, u, e[n + 4], 11, 1272893353),
u = f(u, d, a, c, e[n + 7], 16, -155497632),
c = f(c, u, d, a, e[n + 10], 23, -1094730640),
a = f(a, c, u, d, e[n + 13], 4, 681279174),
d = f(d, a, c, u, e[n], 11, -358537222),
u = f(u, d, a, c, e[n + 3], 16, -722521979),
c = f(c, u, d, a, e[n + 6], 23, 76029189),
a = f(a, c, u, d, e[n + 9], 4, -640364487),
d = f(d, a, c, u, e[n + 12], 11, -421815835),
u = f(u, d, a, c, e[n + 15], 16, 530742520),
a = g(a, c = f(c, u, d, a, e[n + 2], 23, -995338651), u, d, e[n], 6, -198630844),
d = g(d, a, c, u, e[n + 7], 10, 1126891415),
u = g(u, d, a, c, e[n + 14], 15, -1416354905),
c = g(c, u, d, a, e[n + 5], 21, -57434055),
a = g(a, c, u, d, e[n + 12], 6, 1700485571),
d = g(d, a, c, u, e[n + 3], 10, -1894986606),
u = g(u, d, a, c, e[n + 10], 15, -1051523),
c = g(c, u, d, a, e[n + 1], 21, -2054922799),
a = g(a, c, u, d, e[n + 8], 6, 1873313359),
d = g(d, a, c, u, e[n + 15], 10, -30611744),
u = g(u, d, a, c, e[n + 6], 15, -1560198380),
c = g(c, u, d, a, e[n + 13], 21, 1309151649),
a = g(a, c, u, d, e[n + 4], 6, -145523070),
d = g(d, a, c, u, e[n + 11], 10, -1120210379),
u = g(u, d, a, c, e[n + 2], 15, 718787259),
c = g(c, u, d, a, e[n + 9], 21, -343485551),
a = p(a, o),
c = p(c, i),
u = p(u, r),
d = p(d, s);
return [a, c, u, d]
}
function u(e) {
var t, n = "";
for (t = 0; t < 32 * e.length; t += 8) n += String.fromCharCode(e[t >> 5] >>> t % 32 & 255);
return n
}
function d(e) {
var t, n = [];
for (n[(e.length >> 2) - 1] = void 0, t = 0; t < n.length; t += 1) n[t] = 0;
for (t = 0; t < 8 * e.length; t += 8) n[t >> 5] |= (255 & e.charCodeAt(t / 8)) << t % 32;
return n
}
function o(e) {
var t, n, o = "0123456789abcdef",
i = "";
for (n = 0; n < e.length; n += 1) t = e.charCodeAt(n),
i += o.charAt(t >>> 4 & 15) + o.charAt(15 & t);
return i
}
function i(e) {
return unescape(encodeURIComponent(e))
}
function r(e) {
return u(c(d(t = i(e)), 8 * t.length));
var t
}
function s(e, t) {
return function(e, t) {
var n, o, i = d(e),
r = [],
s = [];
for (r[15] = s[15] = void 0, 16 < i.length && (i = c(i, 8 * e.length)), n = 0; n < 16; n += 1) r[n] = 909522486 ^ i[n],
s[n] = 1549556828 ^ i[n];
return o = c(r.concat(d(t)), 512 + 8 * t.length),
u(c(s.concat(o), 640))
} (i(e), i(t))
}
function getpwd(e, t, n) {
return t ? n ? s(t, e) : o(s(t, e)) : n ? r(e) : o(r(e))
}
5.调试加密算法
6.python执行
总结
以上就是几种常见的前端加密算法的处理方式。
往期回顾
走进shellcode
两道挺有意思的CTF题
SQL注入绕过某Dog
评论
